Password-based Key Derivation Function 2 (PBKDF2)
The PBKDF2 (Password-based Key Derivation Function 2) SHA-256 algorithm is used to derive Encryption Keys from the user’s Master Password. The Master Password is hashed locally on the user’s machine, using the user’s email address as a salt and a hashing technique, before being sent to Locker’s servers. When Locker’s servers receive the hashed Master Password, it is hashed once more with a cryptographically secure random salt (generated by the CSPRNG algorithm), along with a hashing technique, and then stored in Locker’s database. The default number of iterations used with the PBKDF2 algorithm is 100,001 iterations on the user’s machine, followed by an additional 216,000 iterations when stored on Locker’s servers (for a total of 316,001 iterations by default).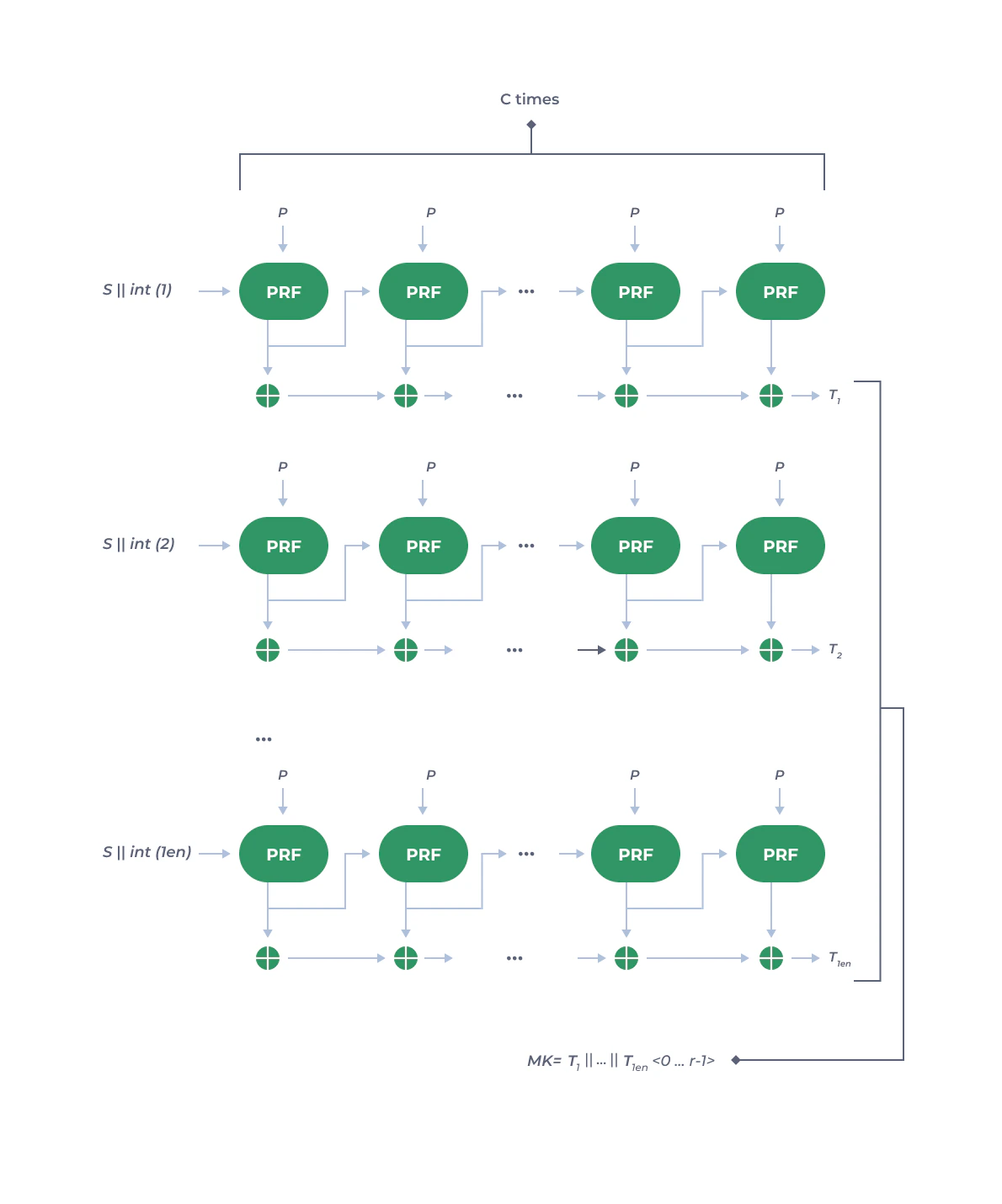
password: the user’s master password.salt: cryptographic salt; here Locker uses the user’s email as the initial salt.iter_count: number of iterations.hash_func: hash algorithm with output length .key_len: desired length of the key.
K is divided into blocks of maximum length . For each block :
- Use the hash function
iter_counttimes with the input beingpasswordandsalt, where the firstsaltis the user’s email, and subsequentsaltvalues are the output of the previous hash:
- Perform an XOR operation with all outputs from step 1:
- Finally, all blocks concatenated together produce the key :